Just a quick note on a recent discovery.
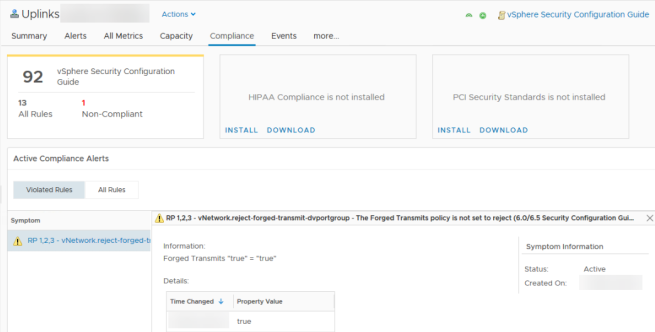
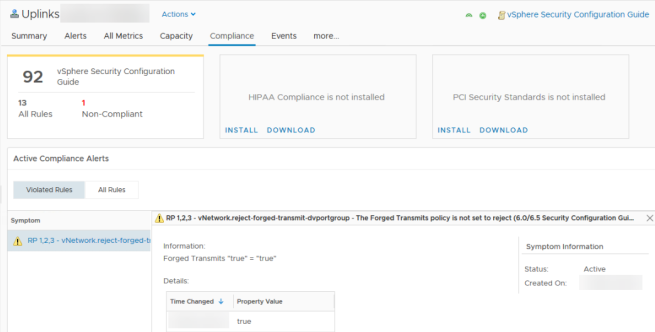
When using the vSphere Security Configuration policy in vRealize Operations Manager you may see an alert similar to the following.
RP 1,2,3 – vNetwork.reject-forged-transmit-dvportgroup – The Forged Transmits policy is not set to reject
Checked the config for the security policy on the port groups using:
Get-VDPortgroup | Get-VDSecurityPolicy
After some digging I found that Forged Transmits is enabled on uplink port groups by default but not on regular port groups. This is because the uplink ports will need to pass traffic (VM, management, etc…) for MACs that are not on the interface.
This alert is a false positive and should be excluded from the compliance checker. Time permitting I will follow up with info on how to do this.
tl;dr – don’t disable forged transmits on uplink port groups, something will break
Here is some good background info on forged transmits: http://wahlnetwork.com/2013/04/29/how-the-vmware-forged-transmits-security-policy-works/
Someone else with the same issue: https://communities.vmware.com/thread/577449